IPv6 World
Project
Video demo
Here is a video demo of ipv6world.
We can see two traceroutes, one to www.kame.net and one to www.freebsd.org. Then a traceroute using routing headers, that go through the
router before www.kame.net to www.freebsd.org is done, then another one going through a router previously discovered on the middle of the path to www.kame.net to another router in the middle of the path to www.freebsd.org. Finaly, a simple traceroute to a router between www.kame.net and www.freebsd.org is done uncovering another path.
Then some searches are done: all the nodes identified as Canadian IP and all the nodes having port 80 open are made pulsing.
About
IPv6world uses rtgraph3D's physics engine. It also recognize all of
its commands, including the submission of new edges. It needs to run a
probe and will interact with it through its stdin/stdout. The probe
can be run through ssh. The probe uses scapy6 and the scapy6 teredo
extention, which means that, to some extent, you can reach the IPv6 backbone
on a box with only IPv4 access.
IPv6 uses 2 sqlite databases. They can be created with the sql scripts
in the db/ directory. The dbnet.db database is designed to hold
informations on IP addresses from whois databases, like country or
network name. The ipdb.db database is used by ipv6world to store
informations on nodes found while exploring the network, like the
reverse DNS, AS name, or open TCP ports, or even edges.
Each time a new node is spawned (from a traceroute or by hand),
attributes are looked for into dbnet and ipdb. Each attribute not
present in ipdb is asked to the probe.
A node can be shift-clicked to be added into the traceroute list. A
node can be control-clicked to be added into the traceroute list, then
run the traceroute through all the nodes into the traceroute list,
then empty the traceroute list.
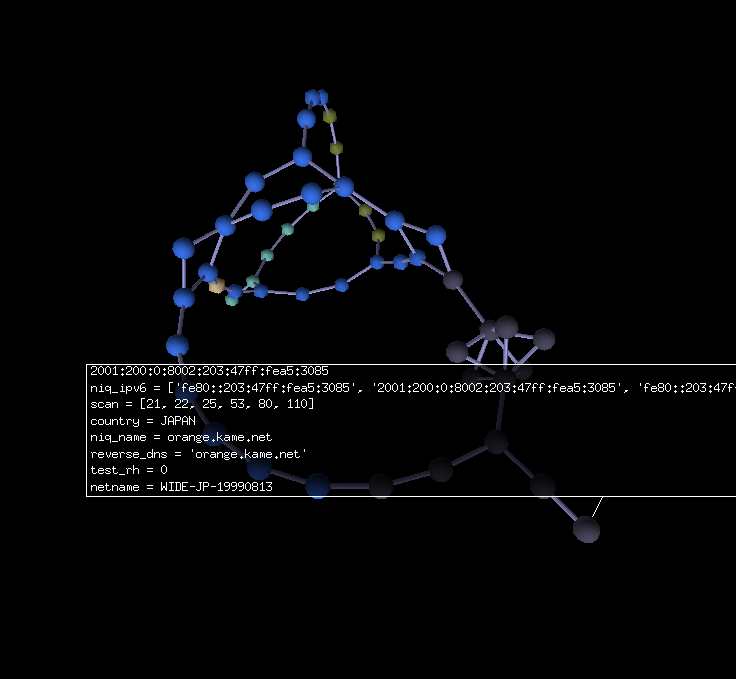
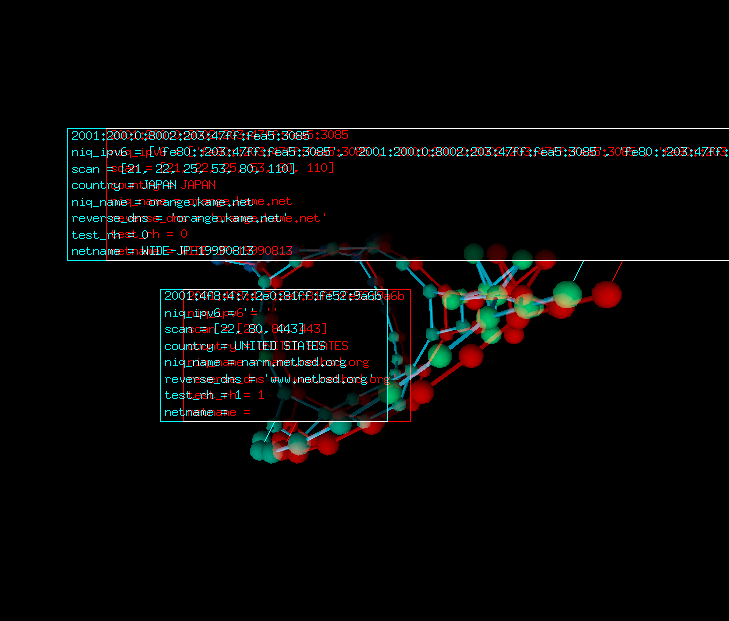
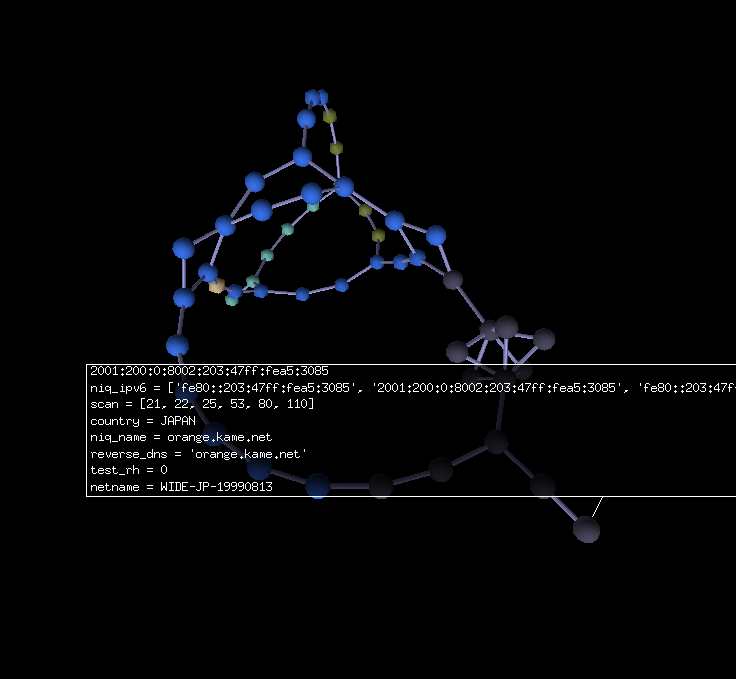
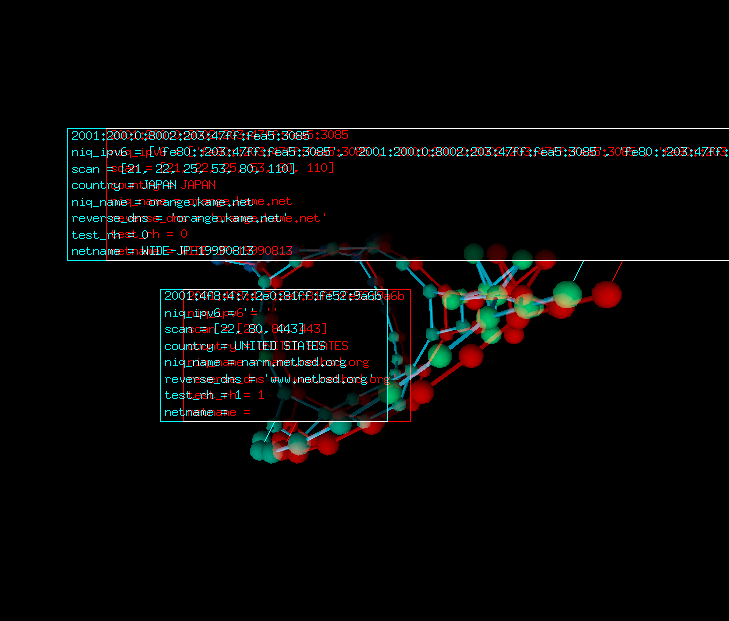
Here is a traceroute to www.kame.net, www.netbsd.org and additional
pathes discovered using routing headers:
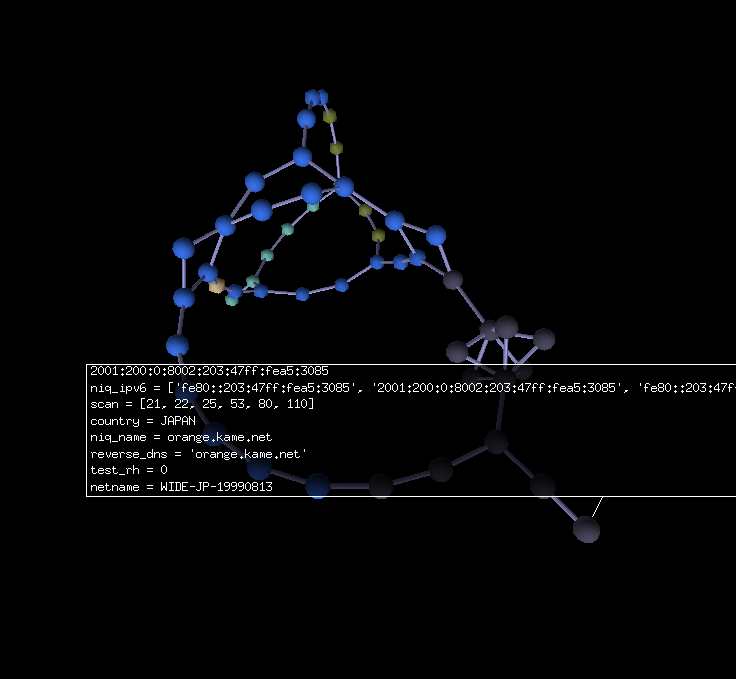
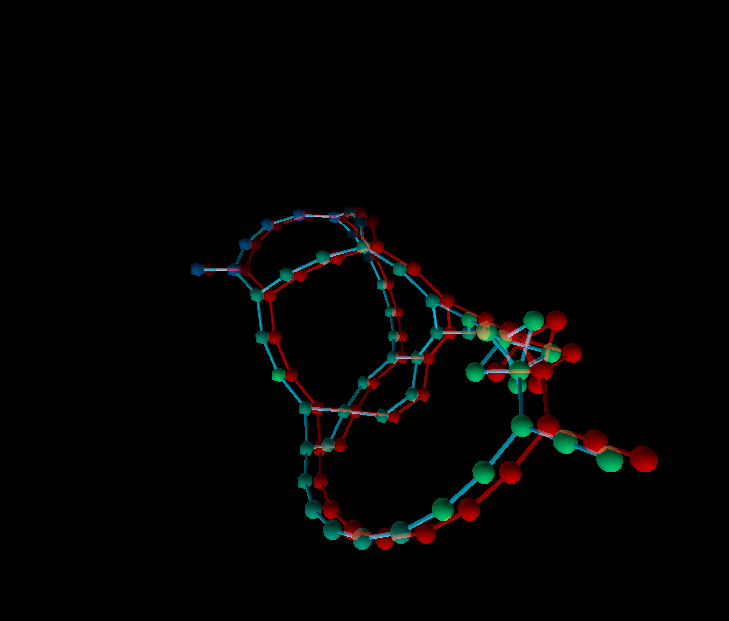
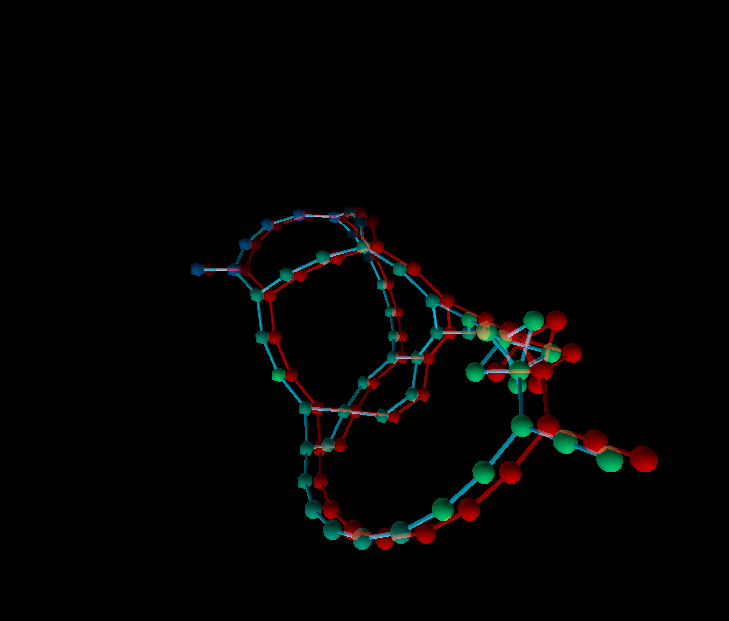
Other views using red/cyan anaglyphs:
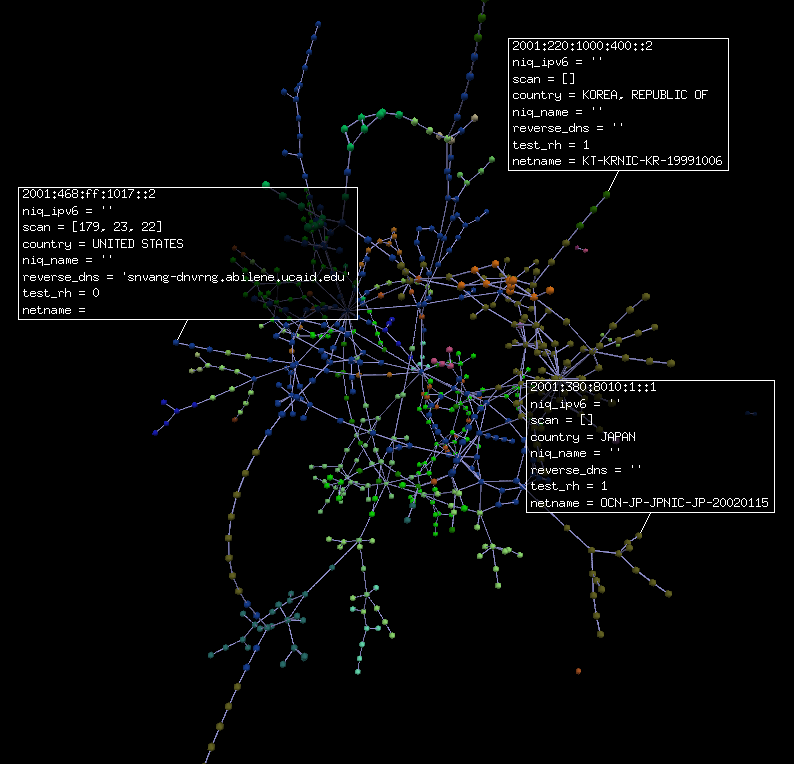
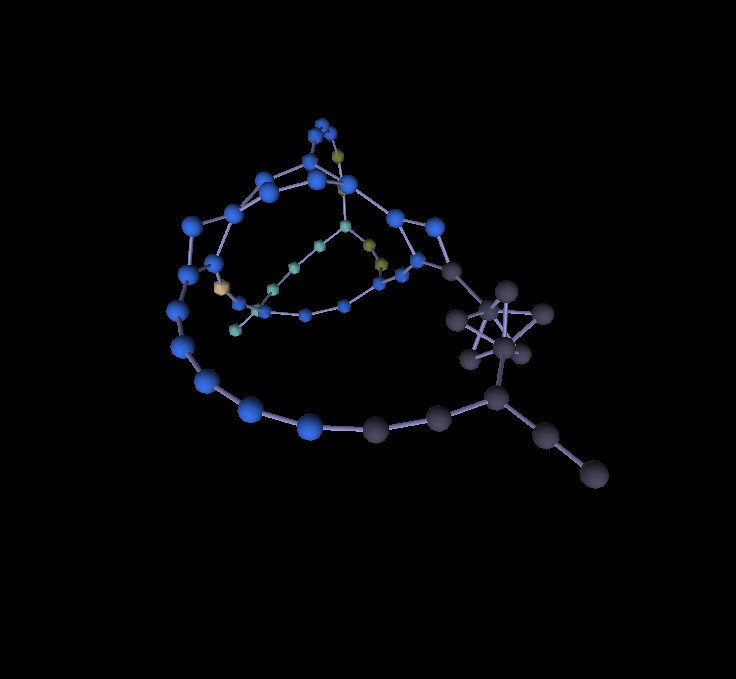
Here are views of a part of the IPv6 backbone:
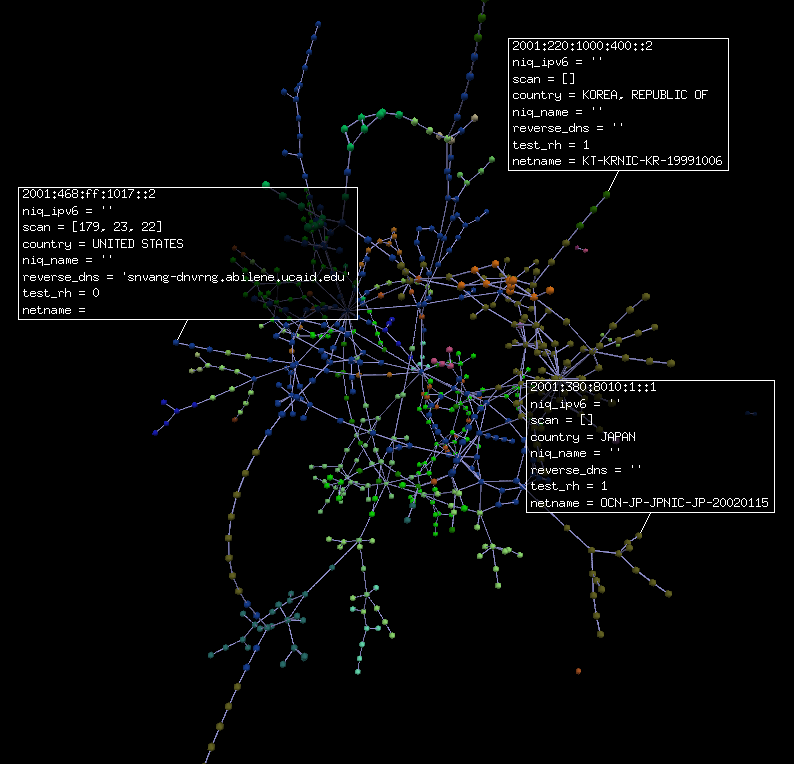
 Let's highlight routers with port 179 open:
Let's highlight routers with port 179 open:
find scan=179
DEBUG: -*-*-*-[ 'find scan=179' ]-*-*-*-
INFO : 395 nodes found

Available commands
- attract <float>: change attraction force
- repuls <float>: change repulsion force
- exec <cmd>: execute a python command (**WARNING** this is bad for
security)
- check: return
- dump <filename>: dump current graph into a file
- dot [<filename>]: dump current graph as a GraphViz .dot file
- quit: quit
- find <regex>: select all nodes whose name match the <regex> and make
them glow
- find <attribute>=<regex>: select all nodes whose <attribute> matches
<regex> and make them glow
- toggle: toggle information box on every glowing node
- unglow: unselect all
- traceroute <ip/name>: runs a TCP traceroute on port 80
- UDP_traceroute <ip/name>: runs an UDP traceroute on port 53
- scan <ip/name>: run a TCP scan on some interesting ports on <ip>
- test_rh <ip/name>: run a Routing Headers Type 0 test (does it honor
them)
- AS <ip/name>: get AS name
- reverse_dns <ip/name>: get the reverse DNS name
- niq_name <ip/name>: runs a Name Node Information Query
- niq_ipv6 <ip/name>: runs an IPv6 Node Information Query
- listen <port>: listen on TCP <port> and get commands from there too
Syntax
$ ipv6world [-s stereo] [-p probe] [-i ipdb] [-d dbnet] [-b]
-p command to run probe. Communication is done through stdin/stdout
-i path to an IP database
-d path to a dbnet database
-b blind mode. Do not visualize anything
-s stereo mode (active, passive, crosseyed, redcyan, redblue, yellowblue)